Protecting Sources in the Digital Age: Advanced Encryption for US Reporters

In 2026, the sanctuary of the “confidential source” faces unprecedented threats from AI-driven forensic surveillance and the looming shadow of quantum decryption.
For online reporters in the United States, traditional digital safety is no longer sufficient; the industry has shifted toward Post-Quantum Cryptography (PQC) and hardened “Zero-Knowledge” architectures.
This update breaks down the critical transition to quantum-resistant encryption and the latest legal developments regarding digital privilege, providing essential security protocols for reporters operating in an increasingly transparent digital environment.
The Evolving Landscape of Source Protection
The digital era presents unprecedented challenges for journalists seeking to protect confidential sources. As surveillance capabilities grow and data breaches become more common, the imperative for robust security measures has intensified significantly.
US online reporters now face a complex legal and technological environment where source anonymity is under constant threat.
Understanding and implementing advanced encryption techniques is no longer optional but a fundamental requirement for ethical and effective journalism.
This evolving landscape necessitates a proactive approach, moving beyond basic security practices to embrace comprehensive strategies that safeguard sensitive communications and data from sophisticated adversaries.
Understanding the Threats to Digital Source Protection
Journalists routinely handle sensitive information that, if exposed, could endanger sources, compromise ongoing investigations, and undermine public trust. The threats range from state-sponsored surveillance to corporate espionage and malicious hackers.
These adversaries employ various methods, including metadata analysis, subpoena requests, and sophisticated hacking tools, to unmask confidential informants.
The interconnected nature of digital communication further amplifies these risks, making every interaction a potential vulnerability.
Therefore, a thorough understanding of these multifaceted threats is the first step towards building resilient defences for digital source protection.
Metadata: A Silent Betrayal
- What metadata reveals: Even encrypted communications generate metadata, such as who communicated, when, and from where. This information can be pieced together to identify sources.
- Legal implications: Law enforcement agencies often obtain metadata without a warrant, circumventing stronger protections for content. This makes metadata a significant weak point in source protection.
- Mitigation strategies: Using VPNs, Tor, and secure messaging apps that minimise metadata collection are critical for journalists.
Government Surveillance and Legal Challenges
The US government possesses extensive surveillance capabilities, often justified under national security pretexts. This includes the ability to compel technology companies to hand over user data or build backdoors into their systems.
Legal challenges to these practices are ongoing, but reporters must operate under the assumption that their communications could be monitored. This makes the use of strong, end-to-end encryption paramount for digital source protection.
Attributing information clearly and understanding the legal frameworks that govern source protection are also vital components of a robust defence strategy.
Foundational Advanced Encryption Techniques
At the core of digital source protection lies robust encryption. End-to-end encryption (E2EE) ensures that only the sender and intended recipient can read messages, rendering them unreadable to intermediaries, including service providers.
Beyond E2EE, reporters must consider encrypting data at rest on their devices, using full-disk encryption, and employing secure file-sharing protocols.
These techniques create layers of security, making it exponentially harder for adversaries to access sensitive information.
Implementing these foundational techniques is the bedrock upon which a comprehensive source protection strategy is built, ensuring the integrity and confidentiality of journalistic work.
Secure Messaging and Communication Platforms
Choosing the right communication tools is paramount for protecting sources. Platforms like Signal offer strong end-to-end encryption, ephemeral messages, and minimal metadata collection, making them ideal for sensitive conversations.
Other tools, such as ProtonMail for email and Jitsi Meet for video conferencing, also provide robust encryption features. The key is to ensure all parties involved in a communication chain use these secure platforms consistently.
Educating sources on the importance and proper use of these secure messaging platforms is an essential aspect of digital source protection.
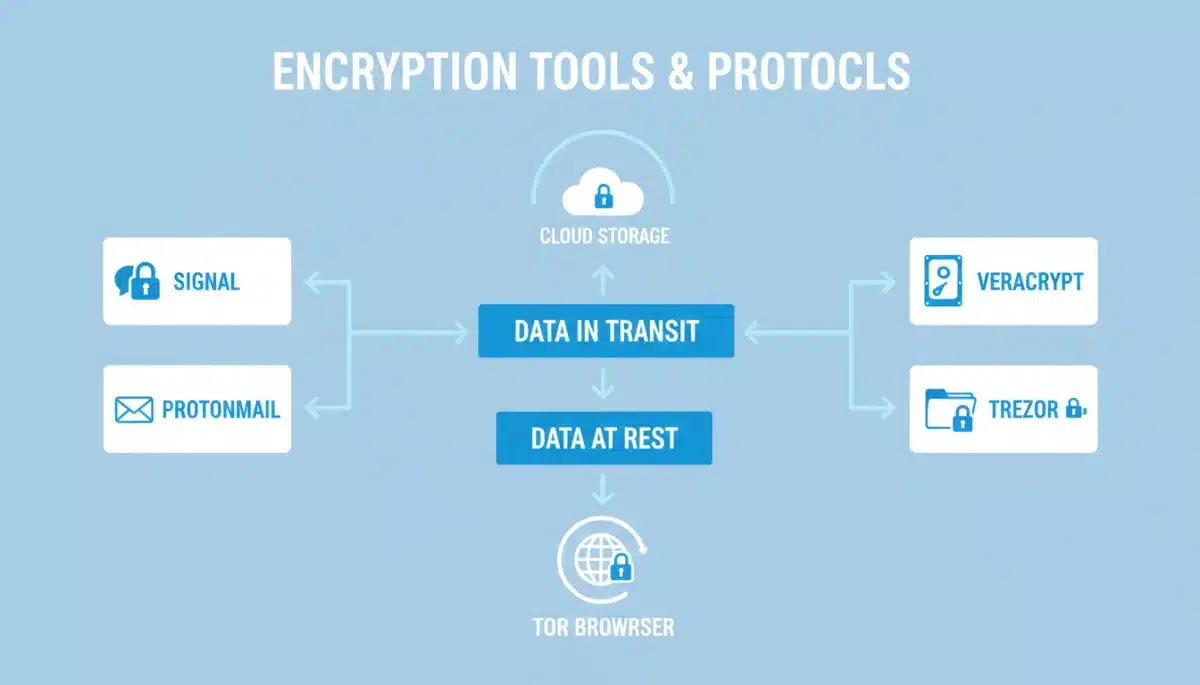
Advanced Encryption for Data at Rest and in Transit
Protecting data stored on devices (data at rest) and data actively being transmitted (data in transit) requires different yet complementary encryption strategies. Full-disk encryption (FDE) is crucial for securing laptops and external drives.
For data in transit, Virtual Private Networks (VPNs) and the Tor network provide anonymity and encrypt internet traffic, preventing interception and location tracking. Combining these methods creates a formidable barrier against digital intrusion.
A multi-layered approach to encryption, encompassing both data states, is indispensable for comprehensive digital source protection.
Full-Disk Encryption (FDE) and Encrypted Containers
- BitLocker/FileVault: Built-in FDE solutions for Windows and macOS, respectively, offer a baseline level of security for device data.
- VeraCrypt: An open-source, cross-platform disk encryption software that creates encrypted virtual disks or partitions, providing plausible deniability.
- Secure USB drives: Encrypted USB drives are essential for transporting sensitive files between secure locations, minimizing exposure during physical transit.
VPNs and Tor for Anonymity and Encrypted Transit
VPNs encrypt internet traffic and route it through a server in a different location, masking the user’s IP address and providing a layer of anonymity. While effective, not all VPNs offer the same level of security or privacy.
The Tor network goes a step further by routing internet traffic through multiple relays worldwide, making it extremely difficult to trace the origin of communications.
Tor is particularly valuable for accessing sensitive information or communicating with sources in high-risk environments, bolstering digital source protection.
However, using Tor requires careful consideration, as its use can sometimes draw unwanted attention, necessitating a balanced approach in its application.
Operational Security (OpSec) Best Practices
Even the most advanced encryption techniques can be undermined by poor operational security. OpSec involves a set of practices designed to protect sensitive information by preventing its inadvertent disclosure through routine activities.
This includes practices such as using strong, unique passwords, enabling two-factor authentication (2FA), regularly updating software, and being mindful of physical security.
A lapse in OpSec can render technological protections ineffective, highlighting its critical role in digital source protection.
Journalists must integrate OpSec into their daily routines, making it a habit rather than an afterthought, to ensure consistent source protection.
Secure Device Management and Updates
Regularly updating operating systems and applications is vital, as updates often include critical security patches that address newly discovered vulnerabilities. Running outdated software leaves devices susceptible to exploitation.
Secure device management also involves encrypting all devices, using strong screen locks, and being cautious about connecting to untrusted networks.
These practices reduce the attack surface for potential adversaries seeking to compromise journalistic integrity.
Implementing a rigorous update schedule and robust device management protocols are fundamental for maintaining digital source protection.
Training and Awareness for Reporters and Sources
The effectiveness of advanced encryption techniques hinges on the knowledge and consistent application by all parties involved. This includes not only reporters but also their sources, who are often less familiar with digital security best practices.
Providing clear, actionable training on secure communication tools, OpSec principles, and the importance of digital source protection is essential. This empowers sources to participate safely and confidently in journalistic endeavours.
Ongoing education and awareness campaigns are crucial to adapt to the rapidly evolving threat landscape, ensuring that both journalists and sources remain vigilant and well-equipped.
Legal Frameworks and Ethical Considerations in 2026
By 2026, the legal landscape surrounding journalist-source confidentiality in the US continues to evolve.
While some states offer shield laws, federal protections remain inconsistent, placing significant onus on reporters to secure their communications technologically.
Ethical considerations also play a crucial role, as journalists have a moral obligation to protect their sources, irrespective of legal mandates. This obligation often drives the adoption of advanced encryption techniques beyond minimum legal requirements.
Navigating these legal and ethical complexities requires constant vigilance and a deep commitment to the principles of digital source protection.
Shield Laws and Federal Protections
Many US states have shield laws that protect journalists from being compelled to reveal their sources. However, these protections vary widely and often have exceptions, particularly in federal cases or those involving national security.
Efforts to establish a comprehensive federal shield law have faced significant hurdles, leaving a patchwork of protections that can be difficult to navigate.
This legal uncertainty underscores the need for robust technological safeguards for digital source protection.
Understanding the specific legal environment in which a story operates is crucial for assessing risk and implementing appropriate security measures.
Future Trends in Encryption and Source Protection
The field of encryption is constantly advancing, with new techniques and challenges emerging regularly.
Quantum computing, for instance, poses a potential future threat to current encryption standards, necessitating the development of post-quantum cryptography.
Decentralised communication networks and privacy-enhancing technologies are also continuously evolving, offering new avenues for secure communication. Staying abreast of these developments is vital for maintaining effective digital source protection.
Anticipating and adapting to these future trends will be key to ensuring that journalists can continue to protect their sources effectively in the long term.
Emerging Technologies and Their Impact
- Post-quantum cryptography: Researchers are developing new encryption algorithms designed to withstand attacks from future quantum computers, a crucial future step for digital source protection.
- Decentralised networks: Technologies like blockchain and peer-to-peer networks offer the potential for more resilient and censorship-resistant communication platforms.
- AI-driven security: Artificial intelligence is being used to enhance threat detection and response, although it also presents new challenges for privacy.
| Key Point | Brief Description |
|---|---|
| Threat Landscape | Journalists face increasing surveillance, metadata risks, and legal challenges to source protection. |
| Core Encryption | End-to-end encryption, full-disk encryption, and secure communication platforms are essential. |
| Operational Security | Best practices like strong passwords, 2FA, and software updates are crucial for safeguarding efforts. |
| Future Outlook | Emerging technologies like quantum-resistant crypto and decentralized networks will shape future source protection. |
Frequently Asked Questions on Digital Source Protection
The most critical step is the consistent use of end-to-end encrypted communication tools like Signal, combined with full-disk encryption on all devices. This dual approach ensures both communications and stored data are secure, forming the bedrock of effective digital source protection against modern threats.
Metadata, such as who contacted whom, when, and from where, is often not encrypted and can be legally obtained without a warrant. While content remains secure, patterns in metadata can reveal associations and identify sources, posing a significant threat to digital source protection.
While built-in features like BitLocker or FileVault are a good starting point, they may not offer the highest level of security or plausible deniability required for sensitive journalistic work. Supplementing them with open-source tools like VeraCrypt and robust operational security practices is recommended for comprehensive digital source protection.
A VPN encrypts internet traffic and masks a reporter’s IP address, adding a layer of anonymity and preventing third parties from monitoring online activity. This is crucial for obscuring the origin of communications and research, contributing significantly to digital source protection.
Source training is paramount. Even the most advanced encryption is ineffective if sources do not know how to use it correctly or maintain good operational security. Educating sources ensures they can participate safely, reinforcing the overall strategy for digital source protection and trust.
Looking Ahead: Sustaining Digital Source Protection
The ongoing commitment to Protecting Sources in the Digital Age is not a static endeavor; it requires continuous adaptation and vigilance.
As technology evolves and new threats emerge, journalists must remain proactive in updating their security protocols and educating their networks.
The integrity of independent journalism hinges on the ability to safeguard confidential information, ensuring that vital stories can continue to come to light without compromising those who bravely share them.
The future of journalism in a digital world depends on these robust protections.
To stay aligned with international standards and evolving legal frameworks, journalists should consult the latest findings on protecting journalism sources in the digital age, a critical resource for maintaining the sanctuary of confidential communication.





